E7
What is E7?
ECDSA DV TLS via ACME.
Suspicious sites — confidence is not always 100%. Use for Threat Hunting or watchlists.
| Last check (UTC) | First seen (UTC) ▾ | URL | Screenshot | Flags | Details |
|---|---|---|---|---|---|
| 2026-06-04 19:30 | 2026-06-03 13:00 |  |
OpenPhish | Details | |
| 2026-06-04 19:30 | 2026-06-03 01:01 |  |
OpenPhish urlscan | Details | |
| 2026-06-04 19:30 | 2026-06-01 13:01 |  |
OpenPhish | Details | |
| 2026-06-04 19:30 | 2026-05-22 13:00 |  |
OpenPhish | Details | |
| 2026-06-04 19:30 | 2026-05-20 13:01 |  |
OpenPhish | Details | |
| 2026-06-04 19:30 | 2026-05-20 01:04 |  |
OpenPhish urlscan | Details | |
| 2026-06-04 19:30 | 2026-05-20 01:03 |  |
OpenPhish | Details | |
| 2026-06-04 19:30 | 2026-05-20 01:02 |  |
OpenPhish urlscan | Details | |
| 2026-06-04 19:30 | 2026-04-24 13:01 |  |
OpenPhish urlscan | Details | |
| 2026-06-04 19:30 | 2026-04-17 01:01 |  |
OpenPhish urlscan | Details |
Suspicious sites — confidence is not always 100%. Use for Threat Hunting or watchlists.
| URL | Screenshot | Flags | Details |
|---|---|---|---|
| http://615.binanceltd.ltd |  |
OpenPhish | Details |
| https://icloudmailservice.svi… |  |
OpenPhish urlscan | Details |
| https://f-binance.com | 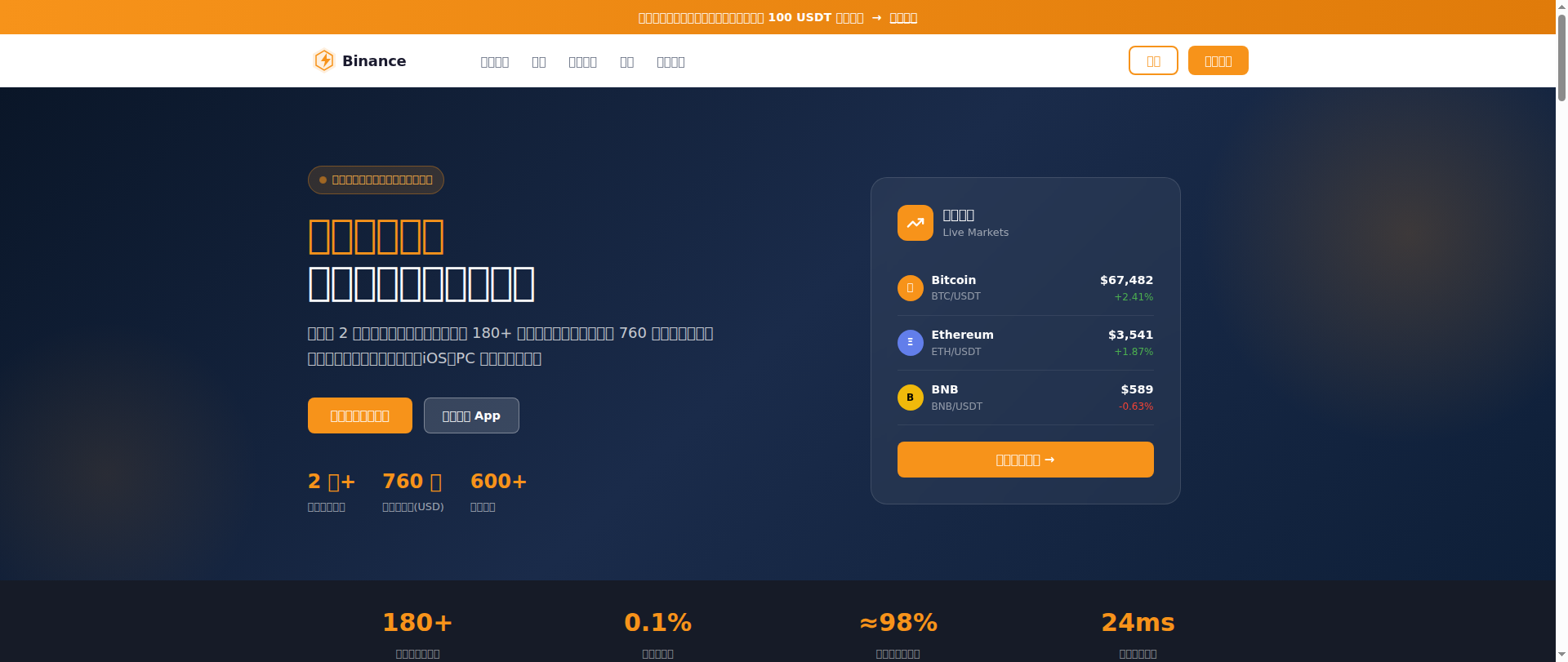 |
OpenPhish | Details |
| https://news-google-chrome.co… |  |
OpenPhish | Details |
| http://fvw0ah.binanceltd.ltd |  |
OpenPhish | Details |
| https://netflixcasino784.com |  |
OpenPhish urlscan | Details |
| http://coinbaseinv.com |  |
OpenPhish | Details |
| http://netflix555-login.com |  |
OpenPhish urlscan | Details |
| https://login.steampowered.co… | 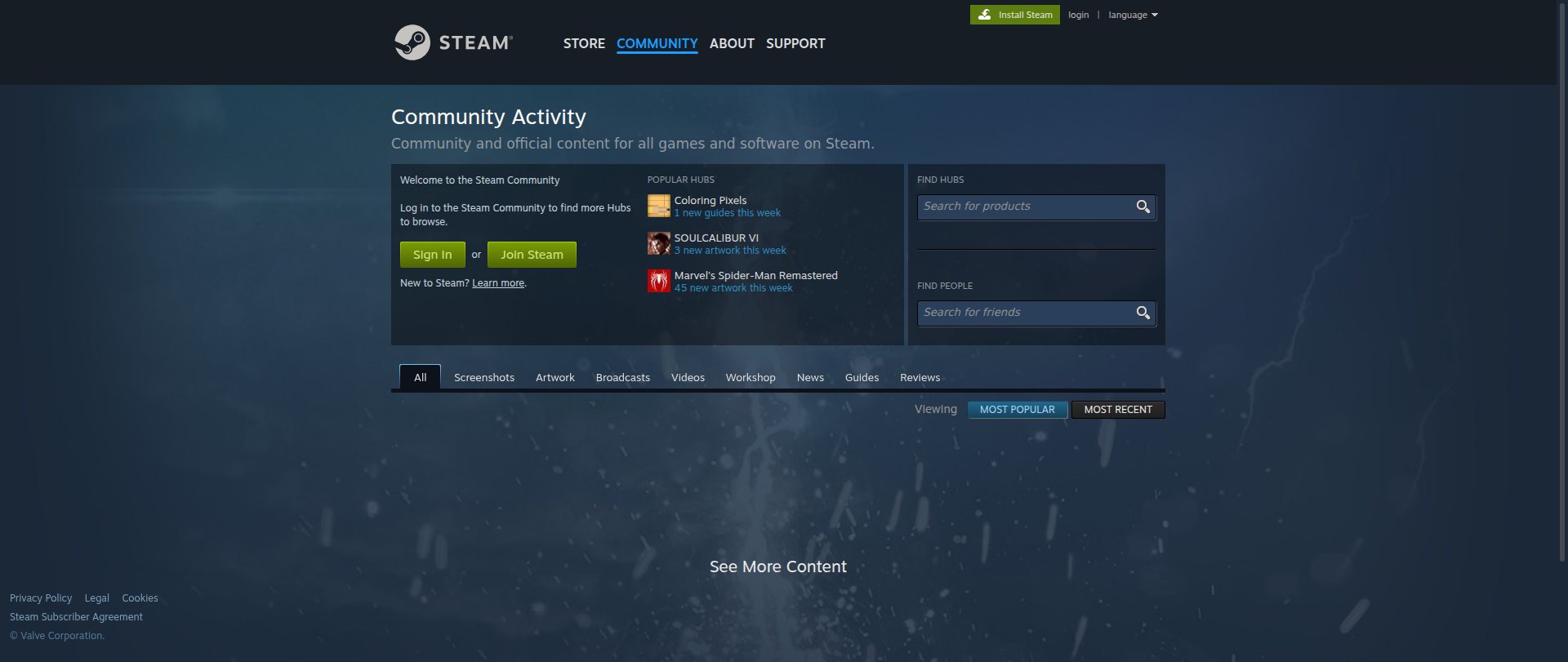 |
OpenPhish urlscan | Details |
| https://login.steampowered.co… | 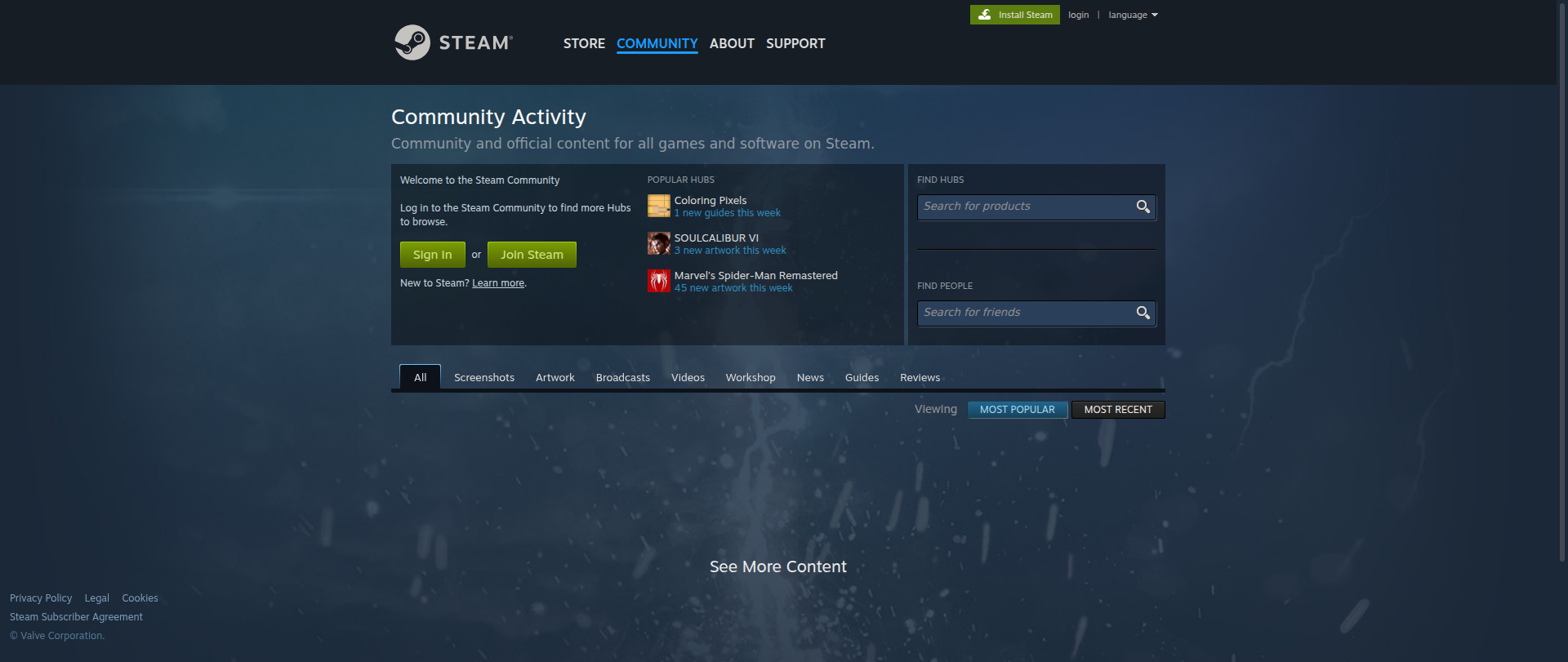 |
OpenPhish urlscan | Details |
Brands most often impersonated with E7
Among the active sites currently using a E7 certificate, these are the brands attackers are mimicking most:
Frequently asked questions about E7
What is E7?
E7 is a publicly trusted intermediate certificate authority operated by Internet Security Research Group (ISRG) and chained to ISRG Root X2. It is recognized by all mainstream browsers and operating system trust stores, so the certificate itself is not a phishing indicator - the same intermediate signs millions of legitimate sites. phishunt only flags the specific domains listed below as suspicious; E7 as a CA is fine.
Is E7 a legitimate certificate authority?
Yes. E7 is a publicly trusted intermediate CA operated by Internet Security Research Group (ISRG), included in the Microsoft, Apple, Google and Mozilla root trust stores. Every mainstream browser automatically accepts certificates it signs. The intermediate itself is not a phishing signal — what matters is the specific domain. phishunt flags only the suspicious domains listed below; E7 keeps signing millions of legitimate sites.
Who runs the E7 certificate authority?
E7 is operated by Internet Security Research Group (ISRG). It is a ECDSA intermediate that chains up to the ISRG Root X2 root, which Internet Security Research Group (ISRG) also owns. Anyone can look up the chain in the public Certificate Transparency logs; the same operator publishes a Certificate Policy / Certification Practice Statement (CP/CPS) describing how issuance and revocation work.
What does E7 mean when my browser shows it as the issuer?
When a browser shows E7 as the certificate issuer for a site, it means TLS was validated through Internet Security Research Group (ISRG)'s ECDSA chain ending at ISRG Root X2. That is normal for tens of millions of legitimate sites that use Internet Security Research Group (ISRG)'s automated DV TLS. The certificate proves the connection is encrypted and that the certificate matches the hostname — it does not prove the site behind it is trustworthy. Always verify the domain name itself.
Why does E7 show up on phishing sites?
Internet Security Research Group (ISRG) issues ECDSA domain-validated certificates automatically and at no cost (or very low cost), which is the exact workflow scammers need to put HTTPS on a throwaway domain. Domain validation only proves that the requester controls the domain name, not that the site behind it is trustworthy. phishunt lists the specific domains currently flagged below — those are the suspicious ones, not E7 itself.
How do I verify a certificate issued by E7?
In a desktop browser, click the padlock in the address bar and open the certificate viewer. Confirm the issuer chain ends at ISRG Root X2, that the subject matches the domain you expect, and that the notAfter date has not passed. A valid E7 certificate only proves TLS was negotiated correctly — always verify the domain name itself belongs to the service you intended to visit.
What is the difference between E7 and E5?
E7 and its siblings (E5, E6, E8) share the same operator (Internet Security Research Group (ISRG)) and roll up to the same root (ISRG Root X2). CAs rotate multiple intermediates so that if one key ever has to be revoked, the damage is contained. As a user, you can treat all of them as the same trust anchor.